Phone Forensics – Bits & Bytes
Cellular forensics can be narrowed down to cell phones forensics, and handheld device forensics. The same procedures are performed and based on similar operating system you can expect similar results.
A complete cell phone forensic examination includes all aspects of available data on the device whether its a simple flip phone, a texting dumb phone or a full blown mini computer rolled up into the smart phone category. The most important fact to be aware of is that full data retrieval is dependent upon the cell phone or PDA model. Deleted data is dependent on when it was deleted and how active the phone user is on reloading new data that will over-write the deleted memory. Don’t forget the first step, external data. Most phones, even basic texting only phones, now have the capability to store data on a Micro SD card.
Don’t forget the SIM. SIM cards are used by GSM phone carriers. A SIM card swill also contain a limited amount of data about standard phone usage. A sim card is not the same as a SD memory card. It is not the same as an LTE card from a CDMA carriers like Verizon to access 4g LTE Data.
AS Technology has grown you now see a SIM card in both GSM and CDMA phones, and you have phones that are unlocked and can work between two carriers using different technologies and different frequencies.
The cell phone forensic examiners at Leverage Investigations will conduct a thorough examination of the data found on the cell phone’s SIM/USIM, the cell phone body itself, and any installed memory cards.
Obtained Data Types
Some of the kinds of data that may be retrieved and examined during a cell phone forensic investigation, even after being deleted, include:
- Call Logs – times, frequency, dialed and received calls, and call duration
- Text messages or SMS messages
- MMS Messages / Picture or Video messages
- Browser History & Internet searches
- GPS locations from cell towers, internet activity or pictures and videos
- Wifi Access locations
- Geo Tagging within images and videos
- Photo Meta data
- Voicemails
- Downloaded App & App Data ( communications within apps)
- Account names & Passwords
- Email Messages, Contact, names & phone numbers
- Address book entries; pictures, birthdays, residential addresses and email addresses
- Photos & graphics
- Videos
- Wi-Fi Connections & passwords
*Deleted data can be recovered in all these categories.
It is not the raw data that is impressive, but the investigative research done with that data to determine, how, what, when, where, how often and more. Often the term “EVERYTHING” can be recovered, but this term is dependent on the specific device model and operating system.
Bring the right Tools
We are certified examiners, the processes and equipment we use are not readily available to a typical investigations firm, we are one of the only firms in Indiana using the cutting edge forensic equipment. We do NOT outsource this service. We have invested resources into this growing field to stay ahead of the curve. There is not just one forensic system we use, we have multiple systems to make sure that we can produce results. There is never just one, do it all tool in any job, cellular forensics is the same way. Don’t bring just a hammer and expect the job to be done right. Our examiners can stand up in court and the data and procedures we use will allow the evidence to be presented on a rock solid base. A single phone record could exonerate you in a criminal charge or any investigation.
Remember with the explosion of the phone industry, the carriers are reducing the records they keep because of the large volume of data. The cellular data once purged from the carrier’s system is gone, unless you have either one of the phones. If you are lucky and do get the last 30 days of text activity, there is no content, just a phone number that a message was sent. Don’t forget that the carrier will not release records to you without a search warrant or court order. Yes, you have to get a court order to get certain records from your own account!
The other thing to remember is that a phone does not use just the cellular connection to communicate. It also has a data connection, so you can still call, text, chat, and do everything else without using the cellular signal, and without generating any activity report with the carrier. That means that if you use a VOIP (Apple Messenger, Facetime, google voice, snap-chat, Facebook, LINE, whats App, Signal, Etc) type of chatting program, phone records from carrier will not show any of that activity. Only a Cellular forensics exam will.
Interesting Facts
Cell phone Statistics
As of January 2014:
- 90% of American adults have a cell phone
- 58% of American adults have a smartphone
- 32% of American adults own an e-reader
- 42% of American adults own a tablet computer
- Cell internet access:
- As of May 2013,
- 63% of adult cell owners use their phones to go online.
- 34% of cell internet users go online mostly using their phones, and not using some other device such as a desktop or laptop computer.
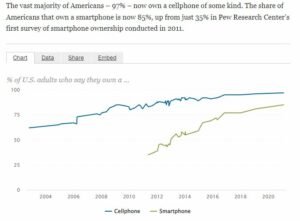
The vast majority of Americans – 97% – now own a cellphone of some kind. The share of Americans that own a smartphone is now 85%, up from just 35% in Pew Research Center’s first survey of smartphone ownership conducted in 2011.
What is a Cellular Extraction
How is a forensics cellular extraction done?
Device must be isolated from any network connection to prevent any changes in the data stored on the device. Any extracted data must be an identical copy of what was on the device. This includes un-allocated (unused or deleted) Space. When you do a copy paste you are only copying the visible file structure, NOT the hidden files and not the un-allocated space. Extraction software must be able to acquire a file system, or image of the device. The Software used must have the capability to then re-organize to copied data (without changing a and allow the examiner to build a forensics report that is easily understood by the common person, as well have a forensic trail (called Hash Marks). The system and procedures used must be commonly accepted within the forensics community. In laymen’s terms, it has to of proven itself with its technology, software, and forensics process. A “new” product will need to be tested and compared with standard results. Then results need to be proven to have been acquired within a forensics means. (did it get data without compromising the evidence).
What is a Forensic Exam
An exam is a slow and methodical investigative sifting and analyzing the data acquired from a forensics extraction. If you are looking for a specific set of parameters then that is not as slow of a process as you would think. To be a forensic exam, everything must be examined and the forensic examiner should not be just capturing one data set to be analyzed and reported on. The data is correlated and bookmarked within the report so it can be easily referenced as evidence. Software and hardware from Cellebrite, Oxygen Forensics, SecureView, Belaksoft, XRY, Paraben, EnCase, and other similar brands provide excellent results. There is never 1 solution that solves all phone forensics exams, restrictions from the device model and operating system version can affect what each varied forensic software can obtain from the records.
Why is a Forensic Method of Extraction Critical
Once that device is connected improperly, anything acquired can be called into question in court. If the software is NOT within the community standards or experimental, it should not be the primary point of information gathering and investigation. If this is a criminal trial, or a substantial civil trial; that could be the difference between freedom or a large financial loss or gain. That data can be considered questionable and that act (improper exam) can taint the evidence within the device itself, a lawyer could argue that the improperly done exam changed the original device records. A forensic device is first design around preserving electronic evidence and NOT altering the data, then copying the unaltered data to a new destination storage media for exam. That copy will match forensic hash marks with the original if the copy needs to be verified. The Forensics process should be repeatable.


